Introduction
A fintech founder sits across from their first enterprise prospect—a Fortune 500 company ready to sign a six-figure contract. The deal stalls during vendor due diligence with a single question: "Can you provide your SOC 2 Type 2 report?"
The founder doesn't have one. The contract is postponed indefinitely while competitors with compliance documentation move forward.
This scenario plays out daily across the startup ecosystem. 98% of Fortune 500 companies require a SOC 2 Type 2 report during vendor onboarding, and missing this documentation adds 2-3 weeks or more to sales cycles.
For fintech and SaaS startups handling sensitive customer or financial data, SOC 2 is no longer optional.
This guide covers:
- What SOC 2 compliance actually means for early-stage startups
- When to start (and why timing affects your audit outcome)
- The step-by-step process from scoping to final report
- What it costs — and how to keep that number manageable
TLDR
- SOC 2 isn't legally required, but enterprise customers, investors, and sponsor banks routinely expect it before signing
- Type 1 reports assess control design at a point in time; Type 2 reports prove operational effectiveness over 3-12 months. Most enterprise buyers require Type 2
- The process covers five steps: scoping Trust Service Criteria, gap analysis, remediation, evidence collection, and an independent audit
- Starting early reduces both audit costs and the opportunity cost of stalled deals—SOC 2 gets harder and more expensive as your organization grows
What Is SOC 2 Compliance and Why Should Startups Care?
The Framework Basics
SOC 2 is an attestation framework developed by the American Institute of Certified Public Accountants (AICPA) for service organizations that collect, process, or store customer data. Unlike self-assessments or security questionnaires, SOC 2 is an attestation verified by an independent CPA firm—not a certification you can award yourself.
That third-party validation — confirming your controls are designed and operating effectively — is exactly why enterprise procurement teams treat it as credible evidence rather than a vendor checkbox.
The Five Trust Service Criteria
SOC 2 evaluates controls across five Trust Service Criteria (TSCs):
- Security (Common Criteria): Protects information from unauthorized access through firewalls, multi-factor authentication, intrusion detection, and incident response. This is the only mandatory criterion.
- Availability: Ensures systems remain operational and accessible through disaster recovery, business continuity planning, and capacity management.
- Processing Integrity: Confirms systems perform intended functions without error through input validation, quality assurance testing, and error handling.
- Confidentiality: Protects sensitive non-PII data using encryption, role-based access, NDAs, and secure data disposal.
- Privacy: Safeguards personally identifiable information (PII) through consent management, privacy policies, and data retention schedules.
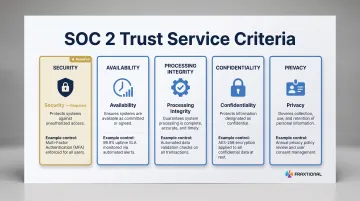
Most startups begin with Security + Availability + Confidentiality, which covers the core controls enterprise customers expect.
Who Needs SOC 2?
Any startup that stores or processes customer data on behalf of third parties should consider SOC 2—especially:
- SaaS companies with enterprise customers
- Fintech platforms handling payment or financial data
- Embedded finance providers
- Crypto firms
- BaaS (Banking-as-a-Service) platforms
Sponsor banks increasingly review SOC 2 posture during partner onboarding. The Federal Reserve, FDIC, and OCC addressed this directly in their 2023 Interagency Guidance on Third-Party Relationships, explicitly advising banking organizations to review SOC reports when evaluating third-party security programs.
Is SOC 2 Legally Required?
No. SOC 2 has no statutory mandate in the United States. However, it has become a de facto commercial requirement. Enterprise customers and institutional partners make it contractually necessary, meaning not having it often disqualifies you before the deal starts.
42% of organizations require vendors to provide SOC 2 or ISO certification, and this percentage climbs significantly higher for financial services companies.
SOC 2 vs. Other Frameworks
Once you know SOC 2 is commercially unavoidable for US enterprise sales, the next question is whether other frameworks belong on your roadmap too. Here's how the main options compare:
- SOC 2: Dominant US-market data security framework; expected by US enterprise buyers
- ISO 27001: International standard, more common in EU/UK markets
- PCI DSS: Required if you process credit card payments directly
- HIPAA: Required only if you handle protected health information
For startups targeting US enterprise clients, prioritize SOC 2 first. There's a 65-75% control overlap with ISO 27001, so if you later expand into EU or UK markets, you won't be starting from scratch — most of the control work carries over.
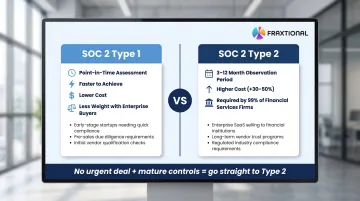
SOC 2 Type 1 vs. Type 2: Which Should Your Startup Pursue?
Understanding Type 1
Type 1 evaluates whether your security controls are designed appropriately at a single point in time. An auditor assesses your control documentation and configuration but doesn't test whether controls operated consistently over time.
When Type 1 makes sense:
- Early-stage startups needing to demonstrate baseline security posture quickly
- Companies building controls for the first time who want a milestone before committing to full Type 2
- Situations where an enterprise deal is in progress and a customer needs immediate compliance signal
Type 1 provides credibility faster but carries less weight than Type 2.
Understanding Type 2
Type 2 evaluates whether controls operated effectively over a defined observation period—typically 3-12 months. Auditors test evidence showing consistent control operation, not just proper design.
Why most customers require Type 2:
- Proves consistency over time, not just a snapshot
- Demonstrates operational maturity and sustained compliance
- 99% of financial services companies and 85% of mid-market enterprises specifically require Type 2
Type 2 costs 30-50% more and requires months of evidence collection — but enterprise procurement teams won't accept anything less.
Decision Framework for Startups
Choose Type 1 if:
- A deal is closing in under 60 days and a prospect needs a compliance signal now
- Your controls went live recently and lack the 3-6 months of evidence Type 2 requires
- Budget is constrained and you need a lower-cost milestone before a full audit cycle
Skip to Type 2 if:
- Your pipeline is predominantly enterprise or financial services buyers
- Controls have been running consistently for 6+ months with documented evidence
- You want to avoid the cost of two separate audits — Type 1 then Type 2 adds up fast
If you're unsure, the deciding factor is usually timeline: no urgent deal pressure and mature controls almost always point toward Type 2 from the start.
Why Delaying SOC 2 Costs Startups More Than They Realize
Sales Cycle Impact
Enterprise and mid-market customers now require SOC 2 reports before executing vendor contracts. Without one, deals stall in security review stages—sometimes indefinitely.
Security reviews add an average of 2-3 weeks to sales cycles, but this understates the problem. Many procurement teams won't even enter evaluation without confirmed compliance documentation, meaning deals never reach the negotiation stage.
The Investor and Sponsor Bank Angle
For fintech startups specifically:
- 81% of private equity firms conduct cybersecurity due diligence as standard practice during transactions
- Sponsor banks often require evidence of security controls before entering BaaS relationships
- Institutional investors now factor compliance posture into funding decisions before funding rounds
For fintech founders, compliance isn't just a checkbox — it's a prerequisite for getting into the room.
The "Smaller Is Cheaper" Argument
SOC 2 cost and effort scale with organizational complexity. A startup with 10 engineers and a focused tech stack faces far less audit burden than one with 100 engineers, multiple product lines, and years of undocumented processes.
Startup opportunity costs for SOC 2 preparation typically fall between $15,000–$60,000, while enterprise costs range from $50,000–$200,000+ due to legacy systems and complex environments.
That cost gap closes fast as your team, product lines, and technical debt grow.
The Opportunity Cost of Reactive Compliance
Startups that scramble for SOC 2 after receiving customer demands often delay deals by 3-6 months. Contrast this with startups maintaining proactive compliance who close security questionnaires immediately.
The compounding effect matters: one closed enterprise deal at the right moment can fund your entire compliance program. Missing that deal because of a 4-month compliance gap has consequences far beyond audit fees.

Understanding the Five SOC 2 Trust Service Criteria
Trust Service Criteria reference table:
| Criterion | What It Covers | Example Control |
|---|---|---|
| Security (required) | Protects information from unauthorized access | Multi-factor authentication, intrusion detection, logging/monitoring |
| Availability | Ensures systems are operational and accessible | Disaster recovery planning, backup processes, capacity planning |
| Processing Integrity | Confirms systems perform intended functions without error | Input/output validation, quality assurance testing, error handling |
| Confidentiality | Protects sensitive non-PII data | Encryption at rest/in transit, role-based access, data disposal procedures |
| Privacy | Safeguards personally identifiable information | Consent management, privacy policies, data retention schedules |
How to Choose Your TSCs
Select Trust Service Criteria based on:
- The data you handle — payment data, PII, financial records, and health information each carry different obligations
- What your enterprise customers explicitly require in contracts or vendor questionnaires
- Regulatory context: Fintech platforms handling payment data should include Availability and Confidentiality
For fintech startups, Security + Availability + Confidentiality represents the standard scope. Bring your auditor into scope decisions early. They'll flag criteria your customer contracts or regulatory environment require that you may not have considered.
How to Get SOC 2 Compliant: A Step-by-Step Startup Playbook
Step 1: Define Scope and Select TSCs
Before anything else, identify which systems, services, and data flows fall within audit scope. A narrowly defined scope reduces audit complexity and cost without sacrificing credibility.
Typically in scope:
- Cloud infrastructure (compute, databases, storage)
- Access control systems
- Customer-facing applications
- Third-party integrations touching customer data
Scoping requirements: The AICPA Description Criteria requires defining infrastructure, software, people, procedures, and data used to provide your service. For cloud/SaaS companies, this includes compute instances, databases, APIs, and vendor integrations.
Step 2: Run a Gap Analysis
A gap analysis compares your current controls against SOC 2 requirements. Key areas to assess:
- Access management (MFA, role-based access, access reviews)
- Encryption (data at rest and in transit)
- Change management (code review processes, deployment approvals)
- Incident response (detection, documentation, remediation procedures)
- Vendor oversight (due diligence, SOC 2 review for critical vendors)
- HR security (background checks, onboarding/offboarding procedures)
Work through each area with a structured checklist — or bring in a compliance advisor who knows what auditors actually look for. Missing basic controls can push certification back months.
Step 3: Remediate Gaps and Implement Controls
Address identified gaps before or during the Type 2 observation period. Prioritize the Common Criteria (Security TSC) first.
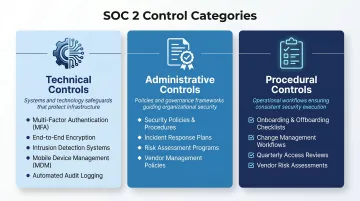
Control types to implement:
Technical controls:
- Multi-factor authentication across all systems
- Encryption for data at rest and in transit
- Intrusion detection and monitoring
- Mobile device management (MDM) solutions
- Automated logging and alerting
Administrative controls:
- Security policies and acceptable use policies
- Incident response plans
- Risk assessment procedures
- Vendor management policies
Procedural controls:
- Employee onboarding/offboarding checklists
- Change management approval workflows
- Quarterly access reviews
- Vendor risk assessments
Step 4: Assign a Compliance Owner
SOC 2 requires ongoing ownership. Someone must maintain controls, track evidence, and coordinate the audit. For resource-constrained startups, this is often where progress stalls.
Many fintech startups address this by working with fractional compliance leadership — a director-level expert who owns the SOC 2 process without the cost of a full-time hire. Fraxtional, for example, places experienced compliance directors directly into this role, keeping the process moving without adding headcount.
Step 5: Collect and Organize Evidence
Auditors will request extensive evidence demonstrating control operation over time.
Typical evidence requirements:
- Access/Logical Security: MFA screenshots, access review records, logs showing access granted/revoked
- HR Security: Background checks, signed employee handbooks/NDAs, security training completion records
- Change Management: Code review documentation, pull request records, change tickets with approvals
- Incident Response: Incident tickets, penetration test reports, vulnerability scan reports
- Vendor Management: Vendor inventory, signed data processing agreements, vendor SOC 2 reports
Compliance automation tools: Platforms like Vanta, Drata, and Secureframe continuously collect and organize evidence — especially valuable during Type 2's extended observation period. They cut collection time considerably, but the controls themselves still need to be properly designed and operating before automation can help.
Step 6: Select an Auditor and Schedule the Audit
Only licensed CPA firms can conduct SOC 2 audits. Choose auditors with relevant industry experience, particularly for fintech or SaaS contexts.
Questions to ask prospective auditors:
- What is your experience with fintech/SaaS companies?
- What observation period length do you recommend for our first Type 2?
- What audit prep materials do you need in advance?
- What is your typical audit timeline from kickoff to final report?
Realistic timeline: From starting gap remediation to receiving your final report typically takes 6-12 months for a first-time SOC 2 Type 2. This includes remediation, a 3-12 month observation period, and audit execution. If speed matters, a 3-month observation window is the minimum for a first Type 2 — enough to satisfy requirements while getting your report out faster.
What Does SOC 2 Compliance Actually Cost Startups?
Cost Breakdown
| Cost Component | Estimated Range (US Startups) |
|---|---|
| SOC 2 Type 1 Auditor Fee | $5,000 - $20,000 |
| SOC 2 Type 2 Auditor Fee | $10,000 - $35,000 |
| Compliance Automation Software | $5,000 - $40,000/year |
| Penetration Testing | $5,000 - $15,000 |
| Readiness Assessment (Optional) | $3,000 - $15,000 |
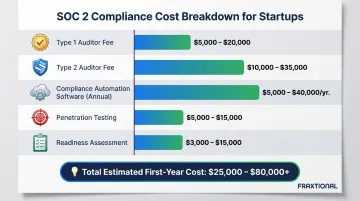
Total first-year costs including readiness, tools, and internal effort typically range from $25,000-$80,000+ for startups.
What Drives Costs Up or Down
Primary cost drivers:
- Adding Privacy or Processing Integrity criteria to your scope pushes costs up fast
- Larger headcount and system complexity increase auditor sampling size and effort
- Type 2 audits run 30-50% more than Type 1 due to extended observation periods
- Undocumented policies mean heavy remediation spend before the audit even starts
- Compliance automation tools cut evidence collection time by 30-50%, lowering overall cost
Internal labor is the cost most startups underestimate. Engineering, legal, and operations teams often log 100+ hours on remediation and evidence gathering. Opportunity costs range from $15,000-$60,000 for startups, depending on who's pulled from other priorities.
Ongoing Maintenance Costs
Annual re-certification, continuous monitoring, and evidence upkeep make SOC 2 an ongoing budget line — not a one-time project.
Startups that automate evidence collection and keep documentation current typically cut recurring audit costs compared to those rebuilding from scratch each year. Budget for annual auditor fees ($8,000-$25,000) plus continued tooling costs.
Frequently Asked Questions
What is SOC 2 compliance for startups?
SOC 2 is an AICPA-developed security attestation framework that verifies how service organizations protect customer data. For startups that collect, process, or store data on behalf of other businesses, it builds trust with enterprise customers, investors, and banking partners through independent validation of security controls.
Is SOC 2 compliance legally required for startups?
SOC 2 is not mandated by law, but it's increasingly required by enterprise clients and institutional partners—including sponsor banks—as a condition of doing business. While not a legal obligation, it has become commercially essential for startups selling to mid-market and enterprise customers.
Who needs SOC 2 Type 2 certification?
SOC 2 Type 2 is most critical for startups selling to enterprise customers, handling sensitive financial or personal data, or seeking investment from institutional investors. 98% of Fortune 500 companies and 99% of financial services firms require Type 2 reports during vendor due diligence.
How much does SOC 2 Type 2 cost for startups?
First-time SOC 2 Type 2 auditor fees for startups typically range from $10,000–$35,000. Total costs including compliance tools, penetration testing, readiness assessments, and internal labor often reach $25,000–$80,000+ in the first year.
How hard is it for startups to get SOC 2 compliance?
The process is substantial but manageable with proper preparation. Main challenges include gap remediation, ongoing evidence collection, and audit readiness—all significantly easier when addressed early rather than after a customer forces the issue.
Which is better, SOC 2 or ISO 27001 for startups?
SOC 2 is generally preferred for US-focused startups—especially fintech and SaaS—due to its market recognition among US enterprise buyers. ISO 27001 suits companies targeting international markets, and since the frameworks share 65–75% control overlap, pursuing both sequentially is efficient once your US compliance foundation is in place.