Introduction
SOC 2 is an audit framework that service organizations use to prove their data security controls actually work. For fintech, SaaS, and crypto companies building compliance programs, the question comes up fast: how often do we need to get audited?
Getting the timing wrong carries real consequences:
- Deals stall when enterprise procurement teams request a current report and find nothing
- Sponsor bank relationships go on hold pending fresh attestation
- Investor confidence drops when a report is outdated during due diligence
- Approved vendor status gets pulled without warning
This guide covers the core questions: the standard cadence for Type 1 and Type 2 reports, which scenarios change that cadence, what actually happens when a report goes stale, and how to build an audit rhythm that supports your business rather than disrupting it.
TL;DR
- SOC 2 Type 2 audits are generally required annually—reports older than 12 months are considered stale by clients and auditors
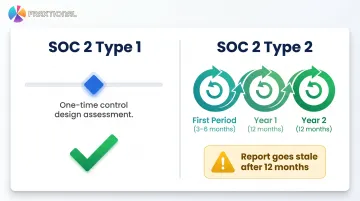
- Type 1 is typically a one-time report done at the start of the compliance journey, not repeated unless major control changes occur
- First Type 2 audit periods are often 3–6 months to get a report in hand faster for active deal cycles
- Security incidents, major infrastructure changes, or new enterprise client requirements can trigger out-of-cycle audits
- SOC 2 bridge letters can cover gaps between reporting periods but are not substitutes for fresh audits
Why SOC 2 Report Timing Directly Affects Your Business
SOC 2 reports are not compliance checkboxes—they are active sales and trust assets. Enterprise clients, sponsor banks, and investors routinely examine the report's coverage period before signing agreements or releasing funds.
Delayed or outdated reports create immediate friction in the sales cycle:
- Security reviews stall while teams wait for current documentation
- Procurement holds deals pending a fresh report
- Prospects may choose a competitor with current attestation
According to Secureframe data cited by SAV Associates (2025), 29% of organizations lost deals for lacking compliance, and 72% underwent audits specifically to win business.
For fintech and crypto companies, sponsor bank relationships and regulatory examinations often require up-to-date SOC 2 evidence. A stale or absent report can jeopardize bank partnerships or trigger remediation demands from regulators. Cross River Bank and Evolve Bank & Trust both require thorough compliance evaluations before launching financial products with fintech partners.
Regulatory enforcement has reinforced these requirements. In 2024, the FDIC issued a consent order to Thread Bank mandating enhanced oversight of its BaaS program, including documented customer due diligence.
How Often Are SOC 2 Reports Required? The Standard Cadence Explained
There is no legal mandate that forces a SOC 2 audit at a specific interval. However, the industry-accepted standard is annual for SOC 2 Type 2. Clients, partners, and auditors treat reports older than approximately 12 months as stale and insufficient evidence of current controls.
SOC 2 Type 1 Frequency
A SOC 2 Type 1 is a point-in-time report that evaluates whether controls are properly designed as of a specific date. It does not cover a period of operating effectiveness.
Most organizations complete a Type 1 once at the start of their SOC 2 journey and don't repeat it unless controls are significantly redesigned or systems change materially.
Some organizations opt for a Type 1 when they need to demonstrate control design quickly — for example, to close a deal — before they have enough operating history for a Type 2. This is a common and accepted approach.
SOC 2 Type 2 Frequency
SOC 2 Type 2 assesses whether controls operated effectively over a period of time. The minimum observation window is approximately 3 months, though 6–12 months is the norm.
Most organizations run a shortened first period (3–6 months) to get a marketable report faster, then move to a rolling 12-month cycle. Enterprise clients — particularly in fintech and banking — increasingly require current SOC 2 Type 2 coverage as a baseline vendor requirement.
Here's what that looks like in practice:
- Reports don't technically expire, but clients, auditors, regulators, and bank partners treat coverage older than 12 months as insufficient
- Coverage gaps create deal risk — a lapsed report can stall a partnership or enterprise sales process
- Aim for continuous coverage — once your SOC 2 journey starts, you should always be either within an active audit window or preparing for the next one
- Treat it as a cycle, not a project — the audit process doesn't end; it renews
When the Annual Cycle Isn't Enough: Scenarios That Change SOC 2 Frequency
The annual cadence is a baseline, not a ceiling. Several business, technical, and regulatory events can and should prompt an out-of-cycle or accelerated SOC 2 assessment.
Based on Major Infrastructure or Control Changes
Significant changes to a service organization's environment can render prior audit findings outdated. Examples include:
- Migrating to a new cloud provider
- Adopting a new data processing system
- Restructuring access control architecture
In these situations, customers may request an updated Type 1 or a new Type 2 to confirm controls are still effective in the changed environment. Under AICPA AT-C section 205, management must disclose "subsequent events"—occurrences such as control changes, acquisitions, or major incidents that take place after the examination period ends but before the report is issued.
Based on Security Incidents or Discovered Vulnerabilities
A confirmed data breach, significant vulnerability, or failed internal control test can each trigger a client or auditor request for a fresh assessment. Enterprise customers and regulators rarely accept a 12-month wait when an active incident is on the table. Common triggers include:
- A breach affecting customer data or system availability
- A discovered vulnerability in a core control
- A failed internal penetration test or control audit
The 2018 updates to AICPA SOC 2 guidance formalize this obligation: management must disclose specific information about security incidents that resulted in a control failure or a failure to meet service commitments.
Based on Client, Bank Partner, or Investor Requirements
Enterprise sales cycles, sponsor bank onboarding processes, and pre-investment due diligence frequently dictate their own reporting timelines:
- A prospective bank partner may require a SOC 2 Type 2 with a coverage period ending within the last 6 months
- A Series B investor may want a fresh report as a condition of closing
- Enterprise clients may demand current reports before contract renewal
These external demands can compress or expand the audit schedule beyond the standard annual cycle.
Based on Regulatory Examination Triggers
For fintech companies operating under state money transmitter licenses or crypto firms subject to regulatory oversight, examination cycles may not align with the company's annual audit calendar — and regulators can request current SOC 2 evidence on their own schedule.
Two regulatory frameworks make this explicit:
- The 2023 Interagency Guidance on Third-Party Relationships directs banking organizations to review SOC reports and independent certifications during vendor due diligence and ongoing monitoring.
- The NYDFS October 2025 Industry Letter explicitly recommends that covered entities review independent third-party assessments (such as SOC 2 or ISO 27001) for third-party service providers.
What Happens When a SOC 2 Report Goes Stale
When a SOC 2 Type 2 report's coverage period ended more than 9–12 months ago, clients and auditors begin questioning whether current controls still match the assessed controls. This creates a credibility and trust gap that can block deals or require time-consuming explanations.
The SOC 2 Bridge Letter Stopgap
A SOC 2 bridge letter is a written assertion from the service organization—not the auditor—stating that controls have not materially changed since the last report's end date and indicating when the next audit is scheduled.
Key limitations:
- Authored by management, not an independent auditor
- Intended for short gaps (ideally never exceeding three months)
- Not a substitute for a full SOC 2 report
- Sophisticated clients, bank partners, or regulators may not accept it for high-stakes decisions
Practical Consequences of Coverage Gaps
A stale report doesn't just slow down a single deal — it can cascade across multiple business relationships at once:
- Enterprise procurement teams may remove the organization from approved vendor lists entirely
- Bank partners may place the relationship on hold until a current SOC 2 report is provided
- Security gaps that emerged during the lapse period go undetected by any independent auditor
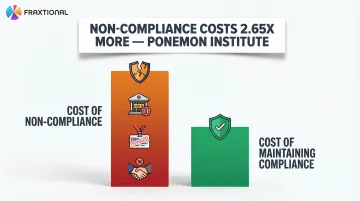
The financial cost compounds quickly. A Ponemon Institute study found that the average cost of non-compliance runs 2.65 times higher than the cost of maintaining compliance — a ratio that has only grown as regulatory scrutiny of fintech and crypto firms has increased.
Best Practices for Managing SOC 2 Audit Frequency
Always Be Under Audit
Plan audit periods so that one window begins immediately after or slightly overlapping with the prior period end date. This eliminates gaps, reduces bridge letter dependence, and demonstrates to clients and auditors that controls are consistently operating — not just tuned up before each review.
Invest in Continuous Monitoring Between Formal Audits
Controls should be tracked and tested on an ongoing basis—not just in the weeks before the audit window closes. This approach:
- Catches deviations early
- Collects evidence throughout the year
- Reduces emergency remediation at audit time
- Reduces audit costs and findings over time
The AICPA Trust Services Criteria (CC4.1, COSO Principle 16) states that the entity must select, develop, and perform ongoing and/or separate evaluations to ascertain whether the components of internal control are present and functioning.
Align the Audit Calendar with Business Cycles
For fintech and crypto companies, schedule audit period end dates to fall before key business milestones — a report that's 10 months old will rarely satisfy a sponsor bank or enterprise procurement team at the moment it matters most. Target period end dates to land before:
- Sponsor bank partnership renewals or new bank applications
- Series A/B fundraising rounds with investor due diligence
- Enterprise procurement cycles requiring vendor security reviews
Fraxtional works with fintech and crypto companies to build audit schedules that align with these milestones rather than defaulting to a generic annual cadence.
Conduct Scoping and Readiness Assessments Before Each Audit Cycle
As a company's technology stack, team, and vendor relationships evolve, take time to confirm scope before each Type 2 period begins. This ensures the audit:
- Captures current risks
- Doesn't miss newly relevant systems or controls
- Reflects actual operating environment
- Avoids costly scope changes mid-audit
Frequently Asked Questions
Frequently Asked Questions
How often are SOC 2 reports required?
SOC 2 Type 2 reports follow an industry-standard annual cadence, though there is no legal mandate. Clients and partners treat reports over 12 months old as stale. Type 1 is typically a one-time report unless major control changes occur.
Is SOC 2 compliance mandatory?
SOC 2 is not legally mandated, but enterprise customers, sponsor banks, and investors routinely require it — and for many fintech use cases, it's a hard contractual condition before they'll contract or fund.
How long is a SOC 2 report valid?
A SOC 2 report does not have a formal expiration date but becomes practically stale after approximately 12 months. Many clients and bank partners require a coverage period end date within the last 6–9 months for sensitive or high-value engagements.
What is a SOC 2 bridge letter and when do I need one?
A bridge letter is a written assertion from the service organization—not the auditor—stating that controls have not materially changed since the last report's end date. Use one to fill short coverage gaps while the next audit is underway — it is not a replacement for a current report.
What is the difference in audit frequency between SOC 2 Type 1 and Type 2?
Type 1 is a point-in-time, typically one-time assessment of control design. Type 2 is a recurring period-based assessment of operating effectiveness, typically renewed annually after the initial shortened first period.
Can my first SOC 2 Type 2 audit cover less than 12 months?
Yes—the minimum observation period is generally 3 months. Many organizations run that first audit over 3–6 months to get a marketable report on the table for sales and deals, then shift to a 12-month rolling period for all subsequent audits.