Introduction
You're six months into building your healthtech platform. Enterprise buyers are asking for your SOC 2 Type II report before they'll sign. A hospital system just sent over a Business Associate Agreement. And your investors want to know which compliance frameworks you're prioritizing before Series A closes.
For fintech and healthtech leaders, SOC 2 and HIPAA often appear on the same procurement checklist. But they're fundamentally different obligations with different enforcement teeth.
SOC 2 is a voluntary security attestation framework developed by the AICPA, designed to prove your security posture to enterprise buyers. HIPAA is a mandatory U.S. federal law governing the handling of protected health information (PHI), enforced by the HHS Office for Civil Rights with penalties reaching $2.19M annually per violation category.
This guide breaks down how the two frameworks differ in scope, enforcement, cost, and timing — so you can build a compliance roadmap that satisfies both buyers and regulators.
TL;DR
- SOC 2 is a voluntary AICPA security framework for service organizations; HIPAA is mandatory federal law for healthcare entities and their vendors
- HIPAA applies if you create, receive, maintain, or transmit PHI
- SOC 2 is typically required by enterprise buyers regardless of industry
- SOC 2 does not replace HIPAA — significant control overlap exists, but legal obligations differ entirely
- Many healthtech and embedded finance companies need both — pursuing them together saves time and resources
What is SOC 2?
SOC 2 (System and Organization Controls 2) is a security reporting framework developed by the American Institute of CPAs (AICPA), designed for service organizations that store, process, or transmit customer data. The result is an auditor-issued attestation report, not a certification.
The Five Trust Services Criteria
SOC 2 evaluates organizations across five Trust Services Criteria:
- Security (mandatory): Protection against unauthorized access — required for all SOC 2 audits
- Availability: System uptime and operational performance
- Processing Integrity: Accurate, complete, timely processing
- Confidentiality: Protection of sensitive information beyond security
- Privacy: Collection, use, retention, and disclosure of personal information
Organizations select which criteria are relevant to their operations, but Security is always required.
SOC 2 Type I vs. Type II
- Type I: Point-in-time assessment of control design as of a specific date
- Type II: Assessment of operating effectiveness over an observation period, typically 3–12 months
The distinction matters to your customers. Enterprise buyers strongly prefer Type II because it demonstrates consistent operational performance over time, not just a snapshot. While the AICPA doesn't mandate a minimum audit period, industry practice typically sees 3-month minimum testing periods, with most organizations undergoing annual 12-month examinations.
Who Needs SOC 2?
SOC 2 is industry-agnostic and legally voluntary — but near-mandatory in practice for:
- B2B SaaS companies
- Cloud infrastructure providers
- Fintech platforms
- Data processors
- Any service organization whose enterprise customers require third-party security assurance before procurement
Without SOC 2, the risks are commercial, not regulatory: lost deals, security questionnaire fatigue, and exclusion from enterprise procurement cycles. There are no government fines — but over 60% of enterprise buyers now require vendor security attestations before signing contracts, making SOC 2 effectively a cost of doing business in B2B markets.
What is HIPAA?
HIPAA (Health Insurance Portability and Accountability Act) is a U.S. federal law enacted in 1996. The Privacy Rule (effective 2003) and Security Rule (effective 2005) form the practical compliance backbone for modern organizations. Non-compliance carries civil and criminal penalties enforced by the HHS Office for Civil Rights (OCR).
What is Protected Health Information (PHI)?
PHI is any individually identifiable health information that includes names, dates tied to an individual, contact details, Social Security numbers, medical record numbers, health plan beneficiary numbers, and biometric identifiers. Combining health data with any of these identifiers creates PHI.
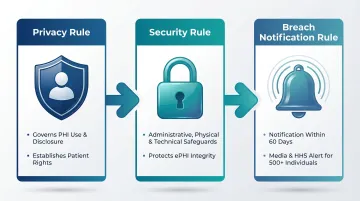
HIPAA's Three Core Rules
- Privacy Rule: Governs how PHI can be used and disclosed; establishes patient rights over their data
- Security Rule: Mandates administrative, physical, and technical safeguards for electronic PHI (ePHI)
- Breach Notification Rule: Requires notification of affected individuals within 60 days of discovering a breach. Breaches affecting 500+ individuals require media and HHS notification.
Who Needs to Be HIPAA Compliant?
HIPAA regulates two categories of entities:
Covered Entities:
- Healthcare providers
- Health plans
- Healthcare clearinghouses
Business Associates: Any organization that creates, receives, maintains, or transmits PHI on behalf of a covered entity, including:
- Cloud storage providers
- Billing services
- EHR vendors
- Analytics platforms
- Payment processors handling health claims
Many fintech and embedded finance companies qualify as Business Associates without realizing it. A payment infrastructure provider processing medical billing transactions, or a financial platform integrated with health insurance workflows, meets the definition. Failure to recognize this status before a breach has resulted in direct OCR enforcement action.
That enforcement is real — and the examples below show how OCR pursues business associates specifically.
Recent HIPAA Enforcement Examples
OCR enforces HIPAA against business associates:
- Comstar, LLC (2025): $75,000 settlement — Ransomware attack affecting 585,621 individuals; OCR found failure to conduct accurate risk analysis
- MedEvolve, Inc. (2023): $350,000 settlement — Unsecured FTP server exposing 230,572 individuals' PHI; OCR cited risk analysis failures and lack of subcontractor BAA
SOC 2 vs. HIPAA: Key Differences
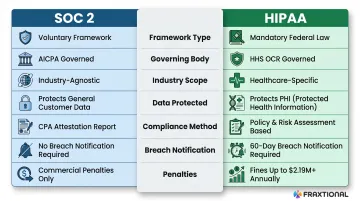
| Parameter | SOC 2 | HIPAA |
|---|---|---|
| Legal Status | Voluntary, market-driven | Mandatory federal law |
| Governing Body | AICPA | HHS Office for Civil Rights |
| Industry Scope | Industry-agnostic | Healthcare-specific |
| Data Type Protected | General customer data | Protected Health Information (PHI) |
| Compliance Process | CPA-issued attestation report | Demonstrated through policies, risk assessments, BAAs |
| Breach Notification | Not mandatory | Required within 60 days |
| Non-Compliance Consequences | Lost business, commercial exclusion | Fines up to $2.19M+ annually per category; criminal exposure |
Legal Weight and Enforcement
HIPAA violations carry tiered civil penalties that adjust annually for inflation. As of January 2026, the ranges are:
- Did Not Know: $145 to $73,011 per violation
- Reasonable Cause: $1,461 to $73,011 per violation
- Willful Neglect (Corrected): $14,602 to $73,011 per violation
- Willful Neglect (Not Corrected): $73,011 minimum, up to $2.19M annually, up to $2.19M annually (criminal charges apply)
SOC 2 has no government enforcement — the penalty is purely commercial: lost deals and procurement exclusion.
Flexibility and Prescriptiveness
- SOC 2 gives organizations flexibility — you choose which Trust Services Criteria to pursue beyond the mandatory Security criterion
- HIPAA defines specific required and addressable safeguards, leaving less room for interpretation
Proposed 2025 HIPAA Security Rule Update: HHS published a Notice of Proposed Rulemaking (NPRM) in January 2025 that would eliminate the "addressable" vs. "required" distinction and mandate encryption, multi-factor authentication, and annual penetration testing. This remains proposed and not final as of April 2026.
No Official HIPAA Certification
Unlike SOC 2, HIPAA has no formal certification process. Organizations cannot become "HIPAA certified." Instead, compliance is demonstrated through:
- Documented risk assessments
- Written policies and procedures
- Workforce training records
- Signed Business Associate Agreements (BAAs)
There's no audit report to show a customer — which makes internal documentation and operational rigor the primary evidence of compliance.
Where SOC 2 and HIPAA Overlap
While legally independent, the frameworks share significant control overlap. Both require:
- Access controls: Multi-factor authentication, role-based access
- Encryption: Data at rest and in transit
- Audit logging: Activity monitoring and system reviews
- Incident response plans: Documented procedures for security events
- Workforce security training: Regular employee education
- Third-party risk management: Vendor due diligence and contracts
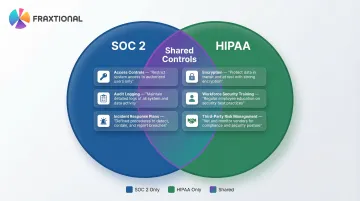
Both frameworks map heavily to NIST standards. The AICPA provides mappings of Trust Services Criteria to NIST 800-53, while HHS and NIST provide HIPAA-to-NIST crosswalks. This means a single well-designed control program can be structured to satisfy requirements under both frameworks simultaneously, reducing duplicate implementation work.
Do You Need SOC 2, HIPAA, or Both?
Three Clear Scenarios
1. B2B SaaS or fintech with no health data → SOC 2 is the priority; HIPAA does not apply
2. Healthcare vendor or any organization handling PHI → HIPAA is mandatory by law; SOC 2 is optional but commercially valuable
3. Healthtech, healthcare-adjacent fintech, embedded finance platforms touching health payments or insurance data → Both are typically required — large healthcare buyers expect a signed Business Associate Agreement (BAA) and a SOC 2 Type II report
The Efficiency Case for Pursuing Both Simultaneously
Because control overlap is substantial, organizations that properly scope a combined compliance program avoid duplicating effort:
- A single risk assessment satisfies HIPAA's risk analysis requirement and SOC 2's risk management criterion simultaneously
- One access control policy — covering MFA and role-based permissions — meets both frameworks' requirements
- A unified incident response plan covers HIPAA's Security Incident Procedures and SOC 2's incident management criteria without separate documentation
The harder question is scoping: edge cases like health payment processing, insurance data integrations, or embedded finance products touching PHI can blur the lines quickly. Fraxtional provides fractional compliance leadership — CCO, CRO, and related roles — to help early-stage and scaling companies work through these decisions without a full-time hire.
Conclusion
SOC 2 and HIPAA address different risks, apply to different entities, and answer to different audiences. They're not in competition — and for some organizations, both apply. The real question is which one your business needs now, and whether you can pursue both without doubling the compliance effort.
Delaying these decisions carries real costs:
- SOC 2 gaps block enterprise deals and slow sales cycles
- HIPAA exposure invites regulatory enforcement and breach liability
- Both signal risk to investors and partners who conduct pre-deal reviews
Getting your compliance program structured early — with experienced guidance — shortens the path to revenue and reduces legal exposure. For fintech and crypto companies navigating these decisions, Fraxtional's fractional compliance leadership model provides the director-level expertise to build the right program without the overhead of a full-time hire.
Frequently Asked Questions
What is the difference between HIPAA compliance and SOC 2?
SOC 2 is a voluntary AICPA security attestation framework for service organizations, while HIPAA is a mandatory U.S. federal law governing protected health information. They differ in legal force, scope, industry applicability, and enforcement consequences.
Does HIPAA require SOC 2 compliance?
HIPAA does not require SOC 2. The two frameworks operate independently, but many healthcare buyers and hospital procurement teams request a SOC 2 report as added assurance, making it commercially valuable for business associates.
Does SOC 2 (Type II) cover privacy requirements?
SOC 2 includes a Privacy Trust Services Criterion covering how personal information is collected, used, retained, and disclosed. That scope is broader than HIPAA's PHI-specific privacy rules, so it does not substitute for HIPAA Privacy Rule compliance.
What is SOC 2 in healthcare?
SOC 2 is used in healthcare by business associates and healthtech vendors to demonstrate security controls to covered entity customers. It complements HIPAA by providing independent attestation of security practices, but does not replace HIPAA compliance obligations.
What are the HIPAA compliance requirements?
HIPAA requires compliance with three core rules: the Privacy Rule (PHI use and disclosure), the Security Rule (administrative, physical, and technical safeguards for ePHI), and the Breach Notification Rule (notification within 60 days). Business Associate Agreements and documented risk assessments are also required.
What is the difference between HIPAA privacy and security requirements?
The HIPAA Privacy Rule governs how PHI can be used, disclosed, and shared, and establishes patient rights over their data. The HIPAA Security Rule sets specific technical, physical, and administrative safeguards required to protect electronic PHI from unauthorized access or breach.