Introduction
Operational risk now accounts for 16.0% of minimum required capital across Group 1 banks globally, according to the Basel III monitoring exercise published in December 2024. Recent enforcement actions underscore the stakes: the OCC issued a $75 million penalty against Citibank in July 2024 for failures in enterprise risk management and internal controls, while TSB Bank faced a £48.65 million fine from UK regulators for operational resilience breakdowns tied to a failed IT migration.
Operational Risk Management (ORM) frameworks are the structured systems banks use to identify, assess, monitor, and mitigate risks stemming from internal processes, people, systems, and external events. Unlike credit or market risk (which focus on borrower defaults or trading losses), operational risk is embedded in every function of a bank. From transaction processing to compliance oversight, it demands fundamentally different governance and measurement tools.
This guide covers the Basel classification system, core framework components, governance structures, measurement tools including RCSA and scenario analysis, and actionable best practices for building or strengthening your ORM program.
TLDR:
- Operational risk drives 16% of regulatory capital for major banks and requires distinct management from credit/market risk
- Basel defines seven event categories, with external fraud surging due to AI and execution failures leading by frequency
- Sound frameworks integrate governance, RCSA, KRI monitoring, and scenario analysis into a single system
- The three-lines model separates risk ownership (business units), oversight (CRO function), and assurance (audit)
- Building proactive ORM culture and GRC technology prevents losses before they occur
What Is Operational Risk in Banks?
Operational risk sits at the center of every bank's risk management program. The Basel Committee formally defines it as "the risk of loss resulting from inadequate or failed internal processes, people and systems or from external events." This definition includes legal risk but explicitly excludes strategic and reputational risk, which banks manage separately.
Why Operational Risk Is Uniquely Difficult
Unlike credit risk (measured through default probabilities) or market risk (quantified via VaR models), operational risk presents distinct challenges:
- Embedded everywhere: Every function—from teller operations to IT infrastructure—generates operational risk exposure
- Hard to quantify: Standard financial models struggle to predict human behavior, system failures, and external shocks simultaneously
- Low-frequency, high-severity: Catastrophic events like the UBS unauthorized trading loss ($2.3 billion in 2011) occur rarely but devastate capital
What Makes Banks Particularly Vulnerable
Banks face heightened operational risk exposure due to:
- Transaction volume: Millions of daily transactions create exponential points of failure
- Digital complexity: Cloud dependencies, API integrations, and cyber threats expand the attack surface
- Regulatory density: BSA/AML, UDAAP, Reg E, and hundreds of other mandates create compliance tripwires
- Third-party dependencies: Outsourced services for payments, cloud hosting, and KYC multiply vendor risk
- Reputational consequences: A single processing outage or data breach triggers regulatory scrutiny, customer attrition, and investor concern at once

The EBA's December 2025 Risk Assessment Report identifies cyber threats, data security, and third-party outsourcing as the most prominent operational risk drivers today, driven by rapid digitization and deepening reliance on cross-border service providers.
The 7 Basel Operational Risk Categories
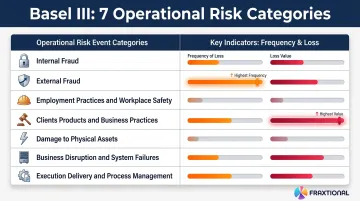
The Basel Committee established seven standardized event-type categories to ensure consistent classification and reporting across jurisdictions. In practice, banks use granular internal taxonomies but report at this level for regulatory capital calculations.
Internal Fraud
This category covers losses from unauthorized activity, asset misappropriation, or regulatory circumvention by employees. Common examples include:
- Unauthorized trading (rogue trader events)
- Theft and embezzlement
- Forgery and document falsification
- Bribery and kickbacks
UBS trader Kweku Adoboli's $2.3 billion loss in 2011 remains the benchmark case — unauthorized trading that resulted in regulatory fines and a seven-year prison sentence.
External Fraud
Third-party-initiated losses — cybercrime, payment fraud, identity theft, and hacking — make up this category. It's growing fast. The ORX Top Risk Review (H2 2025) reports external fraud reached the highest frequency in the database's 22-year history, driven by AI-enabled social engineering scams and digital banking expansion.
Deepfake technology and sophisticated phishing are now sophisticated enough that attribution between internal and external actors has become genuinely difficult to establish.
Clients, Products, and Business Practices
Failures in suitability obligations, KYC/AML compliance, improper business practices, and client information misuse fall here. This category consistently accounts for the largest share of losses by value — driven by the scale of regulatory penalties and the length of associated legal proceedings.
Key conduct risks within this category include:
- Market manipulation, insider trading, and mis-selling
- UDAAP violations and inadequate disclosures
- Failure to meet fiduciary duties
- AML program breakdowns
Business Disruption, System Failures, and Remaining Categories
The four remaining Basel categories round out the taxonomy:
| Category | Scope |
|---|---|
| Business Disruption & System Failures | IT outages, hardware failures, cyberattacks, utility disruptions |
| Employment Practices & Workplace Safety | Compensation disputes, discrimination claims, harassment, workplace injuries |
| Damage to Physical Assets | Natural disasters, terrorism, vandalism, accidents |
| Execution, Delivery & Process Management | Transaction errors, settlement failures, data entry mistakes, vendor disputes |
Execution, Delivery, and Process Management warrants particular attention: ORX data shows it drives the highest frequency of losses across most business lines, making it a priority for control design despite its lower per-event severity compared to conduct risk.
Core Components of a Bank ORM Framework
A sound ORM framework integrates four interdependent architectural elements: governance and risk culture, identification and assessment processes, monitoring and reporting systems, and capital adequacy mechanisms. When these elements operate in isolation, risk accumulates undetected until a stress event exposes the gaps.
Risk Governance and Risk Appetite
The board sets the Risk Appetite Statement (RAS), defining what level and types of operational risk the bank will accept to achieve strategic objectives. The CRO and risk committee translate this appetite into policies, limits, and Key Risk Indicators (KRIs) cascaded across business units.
Governance structures ultimately determine whether staff proactively identify and escalate risks — or let them accumulate quietly. Effective risk culture requires:
- Tone at the top demonstrating accountability
- Clear escalation expectations without retaliation
- Performance frameworks rewarding risk-aware behavior
- Anonymous reporting channels for emerging concerns
The OCC's Spring 2024 Semiannual Risk Perspective emphasizes that appropriate risk culture is the foundation for identifying risks before stress events materialize.
Risk Identification and Assessment
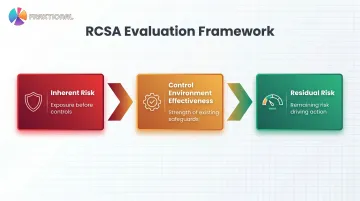
Risk and Control Self-Assessment (RCSA) is the foundational tool for operational risk identification. RCSAs map business processes, identify inherent risks, assess control effectiveness, and produce residual risk ratings that drive management action.
Under the Basel Committee's Principles for Sound Management of Operational Risk (PSMOR 2021), a complete RCSA evaluates three layers:
- Inherent risk — the exposure before any controls are applied
- Control environment effectiveness — how well existing safeguards reduce that exposure
- Residual risk — what remains after controls, which drives management action
Federal Reserve guidance directs internal audit to incorporate RCSA outputs into independent risk assessments.
Where RCSAs rely on historical data, scenario analysis looks forward. Banks use structured workshops to model low-frequency, high-impact events — such as major cyberattacks or widespread internal fraud — and stress-test control environments against exposures that haven't yet appeared in loss records. Basel II mandates scenario analysis as a required input for advanced capital calculations.
Risk Monitoring, Reporting, and Capital Allocation
Key Risk Indicators (KRIs): Early warning metrics that signal emerging risk concentrations before losses occur.
Examples of bank-specific KRIs:
- Transaction error rates by business line
- System downtime frequency and duration
- Staff turnover in key control functions
- Failed trade volumes and settlement exceptions
- Threshold breaches in transaction monitoring systems
KRIs are tiered by materiality for board, management, and operational reporting, with escalation triggers prompting immediate investigation.
Capital Allocation Under Basel III: The Basel Committee replaced the Advanced Measurement Approach (AMA) with the Standardized Approach (SA) to reduce complexity and improve comparability. The SA calculates operational risk capital by multiplying the Business Indicator Component (BIC) by the Internal Loss Multiplier (ILM), which incorporates historical loss data. A mature ORM framework with strong RCSA, loss data, and controls evidence supports more accurate and efficient capital calculations.
The Three Lines of Defense
The three-lines model forms the organizational backbone of ORM governance. The Institute of Internal Auditors updated the framework in 2020, shifting emphasis from purely defensive measures to alignment, collaboration, and value creation.
| Line | Responsibility | Regulatory Expectation |
|---|---|---|
| First Line (Business Units) | Own and manage risks as part of daily operations; implement effective internal controls consistent with risk appetite | Accountable for assessing and managing risks they create |
| Second Line (Independent Risk Management) | Provide oversight, challenge, and framework design; monitor compliance with risk appetite; identify aggregate enterprise risks | Independent of frontline units; oversees risk-taking and measures aggregate exposures |
| Third Line (Internal Audit) | Provide independent assurance to the board on governance, risk management, and internal control effectiveness | Strictly independent; cannot blend with first or second lines |

The Second Line's Role in ORM
The second line, typically led by the CRO function, designs risk policies, maintains the risk taxonomy, reviews RCSA outputs, monitors KRIs, and reports to the board risk committee. This function must remain independent to provide genuine challenge to business units.
Maintaining that independence is a real challenge for smaller institutions. For community banks, FinTechs, and sponsor bank partners, this expertise is increasingly available through fractional leadership models. Fraxtional, for example, provides director-level CRO and BSA Officer services without requiring full-time hires, delivering 50-70% cost savings while maintaining regulatory credibility recognized by sponsor banks, auditors, and regulators.
Fractional CROs bring immediate access to 15+ years of risk management experience and can be officially named in regulatory filings.
Common Governance Failures
The three-lines model breaks down when boundaries blur:
- First-line staff view risk management as a second-line responsibility, abdicating ownership
- Second-line functions become too close to business operations to challenge effectively
- Internal audit lacks independence or sufficient authority
Several structural safeguards help prevent these breakdowns from taking hold:
- Independent reporting lines for second and third lines (directly to board risk and audit committees)
- Periodic audit oversight of risk management effectiveness
- Escalation protocols with mandatory board notification triggers
The OCC's 2024 Consent Order against USAA Federal Savings Bank explicitly cited failures to establish well-defined risk management roles across the three lines.
How Banks Identify and Measure Operational Risk
Banks combine four complementary data and assessment tools—internal loss data, external loss data, scenario analysis, and business environment/internal control factors (BEICFs)—to build a complete view of operational risk exposure.
Internal Loss Data Collection
Banks capture, categorize, and analyze internal loss events by:
- Setting appropriate collection thresholds (typically $5,000–$10,000 minimum)
- Using consistent gross loss definitions before insurance recovery
- Linking losses to Basel event-type taxonomy for regulatory reporting
- Analyzing loss history to identify control weaknesses and recurring failure patterns
- Feeding outputs into capital calculations, RCSA validation, and scenario severity assumptions
External Data and Industry Benchmarking
External loss databases—such as the ORX consortium holding €576.1 billion in gross losses from 1,041,000+ events—supplement internal data for low-frequency/high-severity events where the bank has no direct loss history.
Critical requirement: Banks must filter and scale external data to fit their own risk profile and business model. A $500 million regional bank cannot assume the same cyber loss distribution as a $50 billion global institution.
Key Risk Indicators and Control Monitoring
KRI dashboards enable continuous monitoring between formal RCSA cycles. Banks use them to:
- Set thresholds and escalation triggers for each indicator
- Flag emerging risk concentrations before they materialize as losses
- Calibrate indicators through control testing and effectiveness reviews
For example, if control testing reveals degraded segregation of duties in payment processing, the corresponding KRI threshold should be tightened to reflect that weaker control environment.
Stress Testing and Scenario Analysis
Stress testing uses scenario analysis outputs to estimate potential capital impacts from severe operational events. Results inform:
- Risk appetite limits by business line
- Capital planning and ICAAP documentation
- Contingency response planning (incident response, business continuity)
- Board reporting on tail risk exposures
Regulatory stress tests (such as CCAR for large US banks) incorporate operational risk scenarios alongside credit and market shocks.
Best Practices for Building a Strong ORM Framework
Align with Regulatory Requirements First
Anchor your ORM framework in applicable regulatory standards:
- Basel III Standardized Approach for operational risk capital
- OCC/FDIC supervisory guidance on corporate and risk governance
- BSA/AML program requirements under the Bank Secrecy Act
- UDAAP obligations per CFPB examination procedures
Critical step: Map controls to these requirements explicitly rather than treating regulatory compliance as a downstream check. Document how each control addresses specific regulatory expectations to streamline exams and audits.
Build a Risk-Aware Culture Across All Levels
The people dimension drives ORM effectiveness more than systems or policies. Culture-building initiatives include:
- Training programs tailored by role (frontline risk identification, manager escalation protocols, board oversight)
- Anonymous escalation channels that protect whistleblowers from retaliation
- Frontline engagement in risk identification through RCSA workshops and loss event debriefs
- Performance management frameworks that reward risk-aware behavior, not just revenue generation
Lesson from enforcement: The Treasury OIG report on Wells Fargo's sales practices scandal cited "inappropriate tone at the top" and lack of enterprise-wide oversight as root causes for massive operational failures.
Use Technology to Move from Reactive to Proactive
Spreadsheet-based ORM breaks down when risk events can't be linked to specific business lines, controls can't be tested automatically, and manual aggregation errors distort your loss data. Integrated GRC platforms deliver:
- Automated RCSA workflows that trigger periodic reviews and control testing
- Centralized loss data capture linking events to business lines, processes, and event types
- Real-time KRI dashboards with threshold alerting and trend analysis
- Regulatory reporting automation for Basel, FFIEC, and supervisory submissions
AI and machine learning tools now identify anomalous patterns in transaction data, control monitoring outputs, and incident logs before losses materialize. According to McKinsey's 2025 State of AI survey, nearly 90% of organizations regularly use AI — and operational risk monitoring is emerging as one of the top use cases in financial services.

Treat ORM as a Continuous, Living Program
An ORM framework requires regular review cycles triggered by:
- Internal loss events and near-miss incidents
- Regulatory changes (new guidance, enforcement actions against peers)
- New product launches or market entries
- Third-party relationship changes (new vendors, service terminations)
- Emerging risk themes (AI risk, digital asset exposure, geopolitical disruption)
A designated risk owner with clear authority keeps the program moving between review cycles. Without that executive sponsorship, ORM quietly drifts into a compliance checkbox rather than a strategic capability.
Frequently Asked Questions
What is the operational risk management framework for banks?
An ORM framework is the structured governance, process, and measurement system banks use to identify, assess, monitor, and mitigate risks from internal failures and external events. It's built around Basel Committee operational risk principles, incorporating RCSA assessments, KRI monitoring, scenario analysis, and capital allocation.
What is the RCSA framework for banks?
Risk and Control Self-Assessment (RCSA) is the primary tool banks use to identify inherent risks in their processes, evaluate control effectiveness, and determine residual risk levels. RCSAs assess control design and operating effectiveness across business activities, producing risk ratings that drive remediation priorities.
How to measure operational risk in banks?
Banks measure operational risk using internal loss data (categorized by Basel event types), Key Risk Indicators (KRIs) that provide early warning signals, scenario analysis for low-frequency/high-severity events, and control assessments from RCSAs. Regulatory capital is calculated under Basel's Standardized Approach using business line income and loss multipliers.
What are the 4 pillars of operational risk management?
The four pillars are:
- Regulation — compliance with Basel, OCC, and FDIC frameworks
- People — building risk culture and expertise across all lines of defense
- Process — structured workflows for risk identification, assessment, and escalation
- Technology — systems that automate monitoring, data capture, and reporting
What are the 7 Basel operational risk categories?
The seven categories are: internal fraud, external fraud, employment practices and workplace safety, clients/products/business practices, damage to physical assets, business disruption and system failures, and execution/delivery/process management. Execution failures lead by frequency while clients/products/business practices drive the highest losses by value.
What is an example of operational risk in a bank?
A payment processing system outage delays thousands of customer transfers for six hours, triggering regulatory reporting obligations under FFIEC guidelines, customer compensation requirements under Reg E, and reputational damage — all from a single failure event.