
Introduction
In 2024 alone, federal regulators issued consent orders against multiple BaaS banks—including Piermont Bank, Blue Ridge Bank, Evolve Bank, and Thread Bank—mandating remediation plans with strict timelines, named accountability, and independent validation of corrective actions.
The message is clear: compliance failures carry real consequences. Regulatory fines, sponsor bank terminations, license revocations, and reputational damage can halt growth entirely.
This article is written for fintech companies, crypto firms, embedded finance providers, money transmitters, and banks—particularly those scaling rapidly or operating across multiple jurisdictions. Whether you're preparing for sponsor bank due diligence, investor reviews, or a regulatory examination, conducting a defensible compliance risk assessment is no longer optional.
We'll cover what a compliance risk assessment is, the 5 key steps to perform one, and best practices for regulated financial services environments where rigorous documentation and continuous monitoring are expected.
TL;DR
- A compliance risk assessment identifies regulatory exposure points, evaluates severity, and establishes controls to reduce risk
- Updates are required whenever your business model, regulatory environment, or third-party relationships change
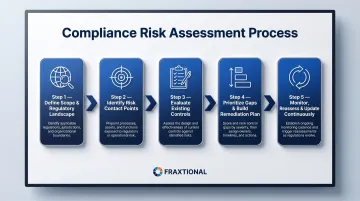
- The 5 steps are: define scope and regulatory landscape, identify compliance risk contact points, evaluate existing controls, prioritize gaps and build remediation plans, monitor and update continuously
- In fintech, high-priority areas include BSA/AML, OFAC, UDAAP, Reg E, state licensing, and crypto obligations
- Sponsor banks, regulators, and investors now expect documented, defensible risk assessments — treat this as a business requirement
What Is a Compliance Risk Assessment?
A compliance risk assessment (CRA) is a structured process organizations use to identify potential regulatory violations, evaluate the likelihood and impact of those risks, and determine whether existing controls are sufficient to manage them.
It's distinct from a general risk assessment (which covers all business risks) and from a compliance audit (which tests whether controls are working). The CRA is the diagnostic step that informs both.
Every effective CRA is built on three core concepts:
- Inherent risk — the raw risk before any controls are applied (for example, operating in high-risk geographies or handling large transaction volumes)
- Risk management — the policies, procedures, and oversight in place to mitigate that risk
- Residual risk — what remains after controls are applied, which must align with the organization's stated risk appetite
A successful CRA produces three outputs that examiners, sponsor banks, and investors all review during regulatory examinations and pre-deal compliance reviews:
- A prioritized view of where the organization is most exposed
- A documented record of control effectiveness
- A remediation roadmap for closing identified gaps
The OCC's Comptroller's Handbook defines inherent risk as "the risk that an activity would pose if no controls or mitigating factors were in place," and residual risk as "the level of risk after controls are taken into account."
The 5 Key Steps of a Compliance Risk Assessment
Step 1: Define Scope and Map Your Regulatory Landscape
The starting point is understanding where the business operates—geographies, products, customer types—and which regulatory regimes apply. For fintech and financial services companies, this means mapping applicable rules:
- BSA/AML and OFAC/sanctions screening
- UDAAP and consumer protection regulations (Reg E, TILA)
- State money transmitter licensing requirements
- Data privacy laws (GDPR for cross-border operations, state privacy laws)
- For crypto firms, applicable FinCEN, SEC, or CFTC guidance
New products, new markets, or new customer segments each expand the regulatory scope and must be explicitly included. Scope should be organized by business lines and products—not just a list of regulations—because process-level differences between business units are critical to capture and are frequently missed in regulation-only assessments.
Step 2: Identify Compliance Risk Contact Points
Once the regulatory landscape is mapped, the next task is identifying specific operations, processes, or transactions where a violation could actually occur—called risk contact points. Practical examples in fintech include:
- Onboarding workflows where KYC/CDD gaps allow high-risk customers through
- Transaction monitoring with AML detection thresholds set too high, missing suspicious activity
- Third-party data sharing that triggers privacy violations when customer data moves without proper consent
- Fee disclosures that create UDAAP exposure when terms aren't clearly presented
- Cross-border payment flows where OFAC screening fails on international transactions
Many teams use a compliance risk matrix or register to document each contact point, the regulation it implicates, the business unit responsible, and an initial risk rating—giving compliance, legal, and operations teams a shared, auditable record.
Step 3: Evaluate Existing Controls
For each identified risk contact point, assess whether a policy, procedure, system control, or manual checkpoint currently exists. Then ask the harder question: is it actually working?
A control that exists on paper but isn't enforced offers no real mitigation.
According to the CFPB Supervision and Examination Manual, a risk assessment must consider "the inherent risks in a particular line of business or the entity as a whole and the quality of controls implemented by the entity to manage and mitigate those risks."
That distinction—between controlled risk and genuine gap—drives the prioritization work in Step 4.
Step 4: Prioritize Risks and Build a Remediation Plan
No organization has resources to fix every gap at once. Risks should be ranked by likelihood (how probable is a violation?) and impact (fines, license revocation, sponsor bank termination). High-likelihood, high-impact gaps with weak controls come first.
Recent consent orders make clear what regulators expect. The FDIC's 2024 order against Piermont Bank requires remediation plans that "list and describe in detail all identified weaknesses and deficiencies," "establish and describe in detail the means by which each identified weakness and deficiency will be addressed and corrected," and "identify the parties responsible for implementing corrective action."
The prioritization output should be documented in a compliance risk report or register with:
- Named responsible parties
- Strict timelines for completion
- Specific means of correction
- Success metrics
This document becomes a key artifact for regulators, auditors, board committees, and investors reviewing the company's compliance posture.
Step 5: Monitor, Reassess, and Update Continuously
The DOJ's guidance for evaluating corporate compliance programs explicitly considers whether a company's risk assessment is current and reviewed periodically—meaning a static, once-a-year document is insufficient.
Trigger events requiring reassessment include:
- New product launches
- Entry into new markets
- Acquisitions or significant partnerships
- Regulatory changes or new guidance
- Enforcement actions in the industry
- Onboarding of new sponsor bank or embedded finance partners
The Federal Reserve's 2024 cease and desist order against Evolve Bank & Trust mandates "a common risk assessment and rating methodology that is regularly updated to account for changes in relevant risk factors." Build a recurring assessment cadence into the compliance calendar. Waiting for an examination or incident to prompt a review is the pattern regulators penalize.
Key Factors That Shape a Compliance Risk Assessment in Fintech and Financial Services
Regulatory Density and Cross-Jurisdictional Complexity
Fintech and financial services companies operate under layered regulatory obligations across multiple jurisdictions. Each layer adds inherent risk, and assessments must explicitly identify where obligations overlap or conflict:
- Federal: BSA/AML, OFAC, UDAAP, Reg E
- State: Money transmitter licenses, state lending laws
- International: GDPR, FCA rules, FINTRAC (Canada)
Companies with multi-jurisdiction operations must scope their CRA to capture all applicable regimes — not just the most familiar ones.
Sponsor Bank and Embedded Finance Relationships
For fintechs operating under a bank sponsor's charter, the sponsor's compliance expectations become direct obligations — not suggestions. Deficiencies identified in the CRA can jeopardize these partnerships, which makes sponsor bank requirements a non-negotiable input to any assessment.
The FDIC's 2024 consent order against Thread Bank requires the board to "review and approve risk tolerance thresholds for individual fintech partners based on an enterprise-wide financial analysis of each FinTech partner's financial projections under expected and adverse scenarios."
Product and Business Model Maturity
New products with unsettled regulatory statusProducts with unsettled regulatory status — BNPL, crypto wallets, earned wage access — carry higher inherent risk because regulatory treatment is still developing. Product age and complexity are standard inputs to inherent risk scoring. Companies launching new products should conduct a targeted mini-assessment before go-live, separate from the broader annual CRA cycle.
Third-Party and Vendor Risk
A compliance failure by a fintech's technology vendor, payment processor, or data provider can create direct regulatory exposure. The 2023 Interagency Guidance on Third-Party Relationships requires banking organizations to maintain "a current inventory of all third-party relationships (and, as appropriate to the risk presented, related subcontractors) that clearly identifies those relationships associated with higher-risk activities."
The CRA's third-party section should document:
- Which vendors touch regulated activities (payments, KYC, data handling)
- Whether each vendor has been reviewed against applicable compliance standards
- How vendor failures would be detected and escalated

Outsourcing a function doesn't outsource the regulatory obligation that comes with it.
Best Practices for an Effective Compliance Risk Assessment
Combine Quantitative Scoring with Qualitative Narrative
Purely numeric assessments (a 1–5 risk score table) often fail to capture nuance—two risks with the same score can have very different root causes and required responses. The most defensible assessments pair a risk matrix with written narratives explaining:
- The inherent risk level and why it exists
- The adequacy of current controls
- The basis for residual risk conclusions
This is what regulators and board committees can actually understand and act on.
Involve Cross-Functional Stakeholders from the Start
Compliance staff should not perform the assessment in isolation. Business line owners, legal, product, and operations leads have the ground-level knowledge of how processes actually work—which is where real risk lives. A cross-functional working group also distributes accountability and builds shared ownership of remediation.
Align the Assessment to the Organization's Risk Appetite
Cross-functional input also makes the risk appetite conversation more grounded. The final step of any CRA is comparing residual risk levels against what the board and senior management have defined as acceptable. Where residual risk exceeds appetite, two options exist:
- Strengthen controls to reduce the likelihood or impact of the risk
- Reduce inherent risk by exiting a high-risk product line or geography
Documenting this alignment makes the CRA useful to the board — and defensible to regulators.
Consider Fractional Compliance Leadership for Resource-Constrained Organizations
Many fintech startups and Series A/B companies lack the internal capacity to conduct a rigorous, board-ready compliance risk assessment. Engaging a fractional Chief Compliance Officer or BSA Officer gives these teams director-level expertise to design and lead the CRA process — without the cost of a full-time hire.
Fraxtional provides exactly this: experienced compliance leaders who can own the assessment end to end and produce documentation that holds up to scrutiny from sponsor banks and investors.
Common Mistakes to Avoid
Three patterns consistently undermine otherwise well-structured compliance risk assessments.
Confusing Inherent Risk with Residual Risk
Inherent risk (risk before controls) and residual risk (risk after controls) are different measures that require separate evaluation. Organizations that skip straight to residual risk routinely underestimate their true exposure — they assume controls are working when those controls have never actually been tested.
Treating the CRA as a One-Time Compliance Checkbox
Filing a completed assessment and moving on is common. It's also dangerous. When business conditions change — new products, new geographies, new partnerships — a stale risk assessment can provide false assurance about risks that have shifted materially since the last review.
Underestimating Third-Party and Vendor Risk Exposure
Fintech teams frequently scope vendor relationships out of the CRA entirely. That creates blind spots. Common exclusions that carry direct regulatory exposure include:
- SaaS compliance tools with access to customer data or transaction records
- Payment processors operating under separate but overlapping regulatory obligations
- Identity verification providers whose control failures become your compliance failures
- Embedded finance partners where data-sharing arrangements are poorly documented

If a vendor's controls are inadequate — or if data is shared outside permitted boundaries — the regulatory exposure lands on your program, not theirs.
Frequently Asked Questions
How do you perform a compliance risk assessment?
Define scope and regulatory obligations, identify specific risk contact points where violations could occur, evaluate existing control effectiveness, prioritize gaps by likelihood and impact, and schedule ongoing monitoring and updates triggered by business changes.
What are the main steps of a risk assessment?
Identify risks, analyze their likelihood and impact, evaluate control effectiveness, prioritize remediation based on criticality, and monitor continuously.
What is a compliance risk assessment program?
A compliance risk assessment program is the formal, recurring process an organization uses to systematically identify, evaluate, and manage its exposure to regulatory violations. It functions as the foundation of an effective compliance management system, informing every policy, control, and oversight decision that follows.
What are the key elements of a compliance program?
Risk assessment, written policies and procedures, training, monitoring and testing, and board/management oversight. The risk assessment comes first — it determines where every other element needs to focus.
What are the key areas of compliance for fintech and financial services?
BSA/AML, OFAC/sanctions screening, UDAAP, data privacy, consumer protection regulations (Reg E, TILA), state licensing (money transmitter laws), and for crypto firms, applicable securities and FinCEN guidance.
What is operational risk and how does it relate to compliance?
Operational risk is the risk of loss from failed internal processes, people, or systems. It overlaps with compliance risk when operational failures lead to regulatory violations, which is why assessing both together produces a more complete picture of exposure.


