
Introduction
Regulatory pressure on fintech, crypto, and banking companies has never been higher. In FY 2025 alone, FinCEN assessed over $1.3 billion in civil money penalties, while the SEC obtained $17.9 billion in monetary relief.
High-profile enforcement actions—including FinCEN's record $3.4 billion fine against Binance and a $1.3 billion penalty against TD Bank—show that compliance failures are no longer just operational setbacks. They're licensing and reputational risks that can shut businesses down.
Most compliance teams know the gaps exist. The harder problem is finding them systematically before an examiner does. This post covers seven best practices auditors need to run compliance audits that hold up—whether you're preparing for a regulatory examination, a sponsor bank review, or a pre-deal investor audit.
TL;DR
- Compliance audits examine whether controls, processes, and documentation meet regulatory requirements
- Effective audits start with clear scope, risk-based prioritization, and standardized evidence collection
- Testing controls operationally, not just reviewing policies, is what regulators expect
- The 5 C's framework (Criteria, Condition, Cause, Consequence, Corrective Action) creates actionable findings
- Continuous monitoring between audits catches real-time risks that scheduled reviews miss
What Is a Compliance Audit and Why Best Practices Matter
A compliance audit is a systematic review of whether an organization's policies, controls, and operations conform to applicable regulatory obligations—such as BSA/AML, UDAAP, Reg E, GDPR, or state money transmitter requirements. Unlike a broader internal audit, which covers operational effectiveness and financial controls, a compliance audit focuses narrowly on regulatory and legal obligations.
Why Best Practices Matter for Fintech, Crypto, and Banking
These sectors face overlapping, fast-evolving regulatory frameworks across multiple jurisdictions—US, UK, EU, and Canada. A poorly executed audit leaves critical gaps undetected until regulators find them, with consequences that include:
- Enforcement actions and consent orders
- License revocations or suspended operations
- Failed sponsor bank reviews that kill partnerships
- Reputational damage that deters investors and customers
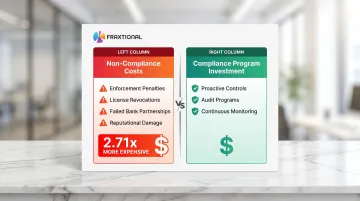
Non-compliance costs 2.71 times more than maintaining a robust compliance program. For organizations operating under BSA/AML, fair lending, or data protection frameworks, that gap translates directly to avoidable penalties, lost partnerships, and damaged investor confidence.
7 Essential Compliance Audit Best Practices
These seven practices apply whether you're conducting an internal audit, preparing for an external regulatory examination, or running a pre-deal compliance review for investors or sponsor banks.
Best Practice 1: Define a Clear Audit Scope and Objectives
Scope creep is one of the most common audit failures. Audits that try to cover everything often surface nothing actionable. Define scope by identifying which regulatory obligations apply, which business lines or processes are in-scope, and what specific controls will be tested.
Regulatory Expectations: The FFIEC BSA/AML Examination Manual requires examiners to "develop a risk-focused examination scope, and document the Bank Secrecy Act/anti-money laundering (BSA/AML) examination plan" based on the institution's risk profile.
Practical Example: For a fintech with a money transmission license, scope might include:
- Transaction monitoring controls for suspicious activity
- SAR filing procedures and documentation
- Customer due diligence records and KYC verification processes
- Compliance with state-specific licensing requirements
This targeted approach ensures audit resources focus on the highest-risk regulatory areas, not the entire business operation.
Enforcement Lesson: FinCEN's 2024 Consent Order against TD Bank explicitly noted that "TD Bank's scope of testing was insufficient relative to the Bank's high-risk customers, products, and services... resulting in trillions of dollars going unmonitored."
Best Practice 2: Apply a Risk-Based Audit Methodology
A risk-based approach allocates audit resources to the areas with the highest likelihood and impact of compliance failure — not equal time across all controls.
High-Risk Areas in Fintech/Crypto/Banking:
- AML program effectiveness and transaction monitoring
- Third-party payment processor oversight
- Cross-border transaction monitoring
- Sanctions screening controls
- Customer due diligence for high-risk customers

Regulatory Mandate: The FFIEC mandates that "independent testing of specific BSA requirements should be risk-based and evaluate the quality of risk management related to ML/TF and other illicit financial activity risks."
Early-stage fintech and crypto firms without dedicated compliance staff often struggle to rank risks accurately. In these cases, the audit scope itself becomes a risk — if no one identifies the high-risk areas upfront, the entire program defaults to low-impact testing.
Best Practice 3: Standardize Documentation and Evidence Collection
Regulators and sponsor banks expect auditors to produce clean, organized, retrievable evidence — not emails or spreadsheets pulled together under pressure. Standardized templates for evidence requests, control testing, and finding documentation create consistency across audit cycles.
What a Standardized Evidence Package Should Include:
- Policy documents with version history and approval dates
- Training completion records by role and date
- Transaction monitoring alerts and disposition logs
- Prior exam findings with remediation status
- Control testing workpapers with sampling methodology
- Interview notes and observation documentation
Regulatory Expectations: The FFIEC states: "Auditors should document the independent testing scope, procedures performed, transaction testing completed, and any findings. All independent testing documentation and supporting workpapers should be available for examiner review."
Best Practice 4: Test Internal Controls — Don't Just Review Them
There's a critical difference between reviewing whether a control exists on paper versus testing whether it actually operates as designed.
Example: A fintech may have a written KYC policy, but testing means verifying that onboarding workflows enforce the policy for a sample of recent accounts — not just confirming the policy document exists.
Control Testing Methods (Per PCAOB AS 2201):
- Inquiry — Interview staff about how controls work
- Observation — Watch the process being performed
- Inspection — Review logs, records, and documentation
- Reperformance — Re-execute a sample transaction through the control to confirm it works
Critical Standard: PCAOB AS 2201 explicitly states: "Inquiry alone does not provide sufficient evidence to support a conclusion about the effectiveness of a control."
Enforcement Reality: Danske Bank pled guilty to fraud for processing billions in suspicious transactions "without appropriate anti-money laundering (AML) policies, procedures and controls in place." Santander UK was fined £107.7 million because it "failed to properly oversee and manage its AML systems" and had "ineffective systems to adequately verify the information provided by customers." Policies existed — but controls failed in operation.
Best Practice 5: Document Findings with the 5 C's Framework
The 5 C's provide a structured method for writing findings that are clear, defensible, and actionable. The Chartered Institute of Internal Auditors defines the framework as:
- Criteria — What the standard requires
- Condition — What was actually found
- Cause — Why the gap exists (root cause)
- Consequence — What risk it creates
- Corrective Action — What needs to change
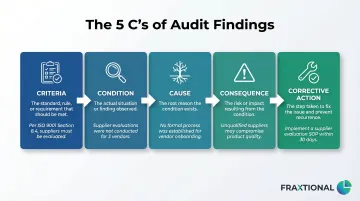
The Accountability Problem with Vague Findings: Vague findings like "controls need improvement" don't create accountability or drive remediation. Findings written with the 5 C's give management a clear picture of the gap, its root cause, and a specific path to resolution.
This framework helps auditors meet IIA Standards 2410 and 2420, which require that communications be "accurate, objective, clear, concise, constructive, complete, and timely."
Best Practice 6: Communicate Findings to the Right Stakeholders in the Right Format
Audit findings die in inboxes when they're not communicated to decision-makers in a usable format.
Tailor Reporting:
- Executive summaries for leadership and boards: risk-rated findings, business impact, strategic implications
- Detailed findings reports for compliance and operations teams: root cause, evidence, remediation steps
- Regulatory-ready documentation if preparing for an exam or sponsor bank review
Management Response Requirement: Audit findings should be presented with a formal management response — requiring the relevant business owner to acknowledge the finding and commit to a remediation timeline. This creates accountability and demonstrates governance maturity to regulators.
Best Practice 7: Build a Corrective Action and Continuous Monitoring Process
An audit's value is measured by what changes after it. A corrective action plan (CAP) turns findings into tracked obligations. Each CAP item should include:
- Owner: The business or compliance lead responsible for remediation
- Deadline: A specific target date, not a vague "Q3 timeframe"
- Success criteria: What operating evidence confirms the control is fixed
- Follow-up test: Confirmation that remediated controls work in practice, not just on paper
The Shift to Continuous Monitoring: Gartner reports that Continuous Controls Monitoring (CCM) can reduce audit time and cost by up to 50% by fast-tracking evidence gathering. Real-time dashboards, automated alerts for control failures, and periodic control sampling prevent compliance gaps from accumulating until the next scheduled audit.
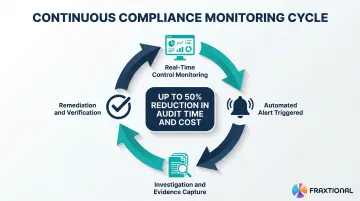
Regulatory Perspective: The OCC's 2024 Semiannual Risk Perspective warns that "data governance gaps and customer or transaction exclusions in BSA/AML transaction monitoring may result in increased noncompliance with requirements to report potentially suspicious activity."
Common Compliance Audit Mistakes to Avoid
Auditing Without Independence
When the compliance team audits itself or when audit findings are reviewed only by the same people responsible for the controls being tested, objectivity is compromised.
The FFIEC mandates that "independent testing should be conducted by the internal audit department, outside auditors, consultants, or other qualified independent parties... the party conducting the BSA/AML independent testing should report directly to the board of directors or to a designated board committee."
For organizations without a separate internal audit function, engaging a fractional compliance officer with no operational stake in the outcome preserves objectivity and gives findings the credibility regulators expect.
Treating the Audit as a One-Time Event
Organizations that only run compliance audits when a regulator requests them or when a new product launches are reactive rather than prepared — and regulators notice.
Establish a structured annual audit program with interim monitoring checkpoints tied to your risk profile. The FFIEC notes there is no fixed regulatory frequency for BSA/AML independent testing, but that "independent testing, including the frequency, should be commensurate with the ML/TF and other illicit financial activity risk profile of the bank." In practice, that means higher-risk institutions should be auditing more often — not waiting for an exam to prompt action.
Failing to Close the Loop
Finding issues without tracking remediation to completion is the most common reason organizations receive repeat findings in regulatory examinations.
Every finding needs:
- An assigned owner
- A committed deadline
- A verified close-out—not just an acknowledgment
The OCC Consent Order against TD Bank cited that the bank "repeatedly failed to take appropriate and timely corrective action to address the highly suspicious activity and failed to properly emphasize BSA/AML compliance."
Conclusion
Executing compliance audits well requires a repeatable, structured approach—from scope definition and risk prioritization through to finding documentation, stakeholder communication, and remediation tracking. For fintech, crypto, and banking companies operating under overlapping regulatory frameworks, these seven practices are the foundation of a defensible compliance program.
For organizations that don't yet have dedicated compliance leadership to design and run a rigorous audit program, Fraxtional provides fractional CCO, BSA Officer, CAMLO, and MLRO services, bringing director-level compliance expertise without the overhead of a full-time hire.
Whether you're preparing for a regulatory examination, a sponsor bank review, or a pre-deal investor audit, Fraxtional helps you build a program that holds up under scrutiny—so findings are documented, remediation is tracked, and regulators see a program that runs the way it should.
Frequently Asked Questions
What are the best practices for compliance audit management?
Effective compliance audit management comes down to five core practices:
- Define audit scope around risk, not just regulatory checklists
- Apply a risk-based methodology to prioritize testing
- Standardize documentation and evidence collection across engagements
- Test controls operationally — don't just review written policies
- Track remediation through to verified close-out, not just acknowledgment
What are the 5 C's of audit findings?
The 5 C's structure every audit finding around five elements:
- Criteria — the standard or requirement that applies
- Condition — what the auditor actually found
- Cause — the root reason the gap exists
- Consequence — the risk or exposure it creates
- Corrective Action — the specific change required
Together, these make findings specific, actionable, and traceable.
How often should a compliance audit be conducted?
Frequency depends on regulatory requirements and risk profile. High-risk areas like AML or transaction monitoring may require quarterly testing, while lower-risk controls can be reviewed annually. Most compliance programs combine an annual audit with continuous monitoring to stay ahead of emerging gaps.
What is the difference between a compliance audit and an internal audit?
An internal audit broadly covers operational effectiveness, financial controls, and governance across the organization. A compliance audit specifically assesses whether the organization meets applicable regulatory and legal requirements such as BSA/AML, UDAAP, or data protection laws.
How do fintech and crypto companies prepare for a regulatory compliance audit?
Strong preparation covers four areas:
- Run a pre-audit gap assessment to surface issues before the examiner does
- Organize documentation so evidence is retrievable, not just stored
- Confirm all prior exam findings are fully remediated with evidence
- Ensure staff can articulate their compliance responsibilities and control ownership clearly
What are the 4 pillars of ITGC?
IT General Controls (ITGC) rest on four pillars:
- Access Management — restricting system access to authorized users only
- Change Management — ensuring system changes are authorized, tested, and documented
- Computer Operations — confirming that processing operations run as intended and are monitored
- Program Development — controls governing the software development lifecycle


