Introduction
When NYDFS fined Infinity Insurance $2.25 million for failing to include customer-facing applications in their risk assessment, the message was clear: regulators don't just review your technical controls. They scrutinize whether documented, enforceable policies govern those controls. For fintech, banking, and crypto companies, a security policy gap is a compliance gap.
Sponsor banks, auditors, and regulatory examiners assess governance through policy documentation. Without documented policies that establish rules, responsibilities, and controls, even robust technical defenses can fail due diligence or trigger enforcement actions.
This guide covers:
- What compliance-ready security policies actually look like
- The essential components that withstand regulatory scrutiny
- A step-by-step development process
- How to map policies to BSA/AML, NIST 800-53, GDPR, PCI DSS, and sector-specific frameworks
TLDR
- Security policies are formal documents governing information asset protection and regulatory compliance
- Compliance-ready policies must map to relevant frameworks — NIST 800-53, GDPR, PCI DSS, BSA/AML, and others depending on your sector
- Effective policies define purpose, scope, roles, access controls, incident response, and enforcement with regular reviews
- Most compliance failures trace back to outdated policies, weak enforcement, or drift from the regulatory frameworks that govern your operations
What Are Security Policies and Why Does Compliance Depend on Them?
A security policy is a formal document establishing rules, responsibilities, and controls for protecting information systems and data. NIST SP 800-53 defines these within control families like Planning (PL) and Incident Response (IR), describing how controls are implemented and documented. These policies form the governance backbone that compliance audits assess.
Three Essential Policy Layers:
- Program-level policies: Set organization-wide security posture — who owns risk, what the tolerance is, how governance flows
- System-specific policies: Define controls for particular environments, such as cloud infrastructure, payment systems, or customer data platforms
- Issue-specific policies: Address specific security concerns like acceptable use, remote access, and password management
A compliance-ready program requires all three layers working together, not standalone documents.
The CIA Triad and Regulatory Mapping:
Security policies protect Confidentiality, Integrity, and Availability — the CIA triad. Each pillar maps directly to specific regulatory obligations, which is why regulators treat undocumented controls as gaps regardless of technical implementation.
| CIA Principle | Regulatory Framework | Requirement |
|---|---|---|
| Confidentiality | GDPR Article 5 & 32 | Personal data processed with appropriate technical measures preventing unauthorized access |
| Integrity | SOX Sections 302 & 404 | Internal controls ensuring financial data accuracy and preventing unauthorized modification |
| Availability | EU DORA Articles 9 & 12 | ICT systems designed for resilience, continuity, and guaranteed accessibility |

Compliance Is Not a Byproduct—It's the Goal
Security protects assets; compliance proves you do it consistently according to external requirements. A policy bridges the two.
The OCC assessed an $80 million penalty against Capital One for failing to establish effective risk assessment processes — a direct consequence of technical controls without documented governance to support them.
Key Components of a Compliance-Ready Security Policy
Purpose and Scope
Compliance-ready policies begin with precise Purpose and Scope sections identifying:
- Systems and data types covered
- Geographic jurisdictions
- Applicable personnel
- Regulatory obligations
For companies operating across the US, UK, Canada, or EU, scope must account for cross-border differences—GDPR applicability for EU data subjects, NYDFS Cybersecurity Regulation for New York-licensed entities.
Roles and Responsibilities
Regulators expect clearly designated accountability. NYDFS cited Block, Inc. because its Information Security Policy was approved by the CISO rather than the Board of Directors, violating 23 NYCRR 500.3.
Each policy needs:
- A named officer responsible for information security (CCO, BSA Officer, or CISO)
- Role-specific responsibilities for policy implementation
- Board-level approval and oversight
- Documented accountability chains
Gaps in documented ownership consistently surface as audit findings — and they're among the easiest deficiencies to prevent.
Access Control
Frameworks like NIST 800-53, PCI DSS, and most bank-facing compliance programs require documented access controls:
- Least-privilege access provisioning
- Multi-factor authentication (MFA)
- User provisioning and de-provisioning procedures
- Periodic access reviews
Verizon's 2025 Data Breach Investigations Report found that in the Financial and Insurance sector, 74% of breaches involved System Intrusion and Social Engineering, with threat actors exploiting the lack of mandatory MFA. Sponsor banks apply especially close scrutiny to access control documentation during fintech due diligence.
Incident Response Plan
Regulatory frameworks specify breach notification timelines and response requirements:
- GDPR Article 33: 72-hour breach notification to supervisory authorities
- NYDFS Part 500: 72-hour electronic notification to superintendent
- BSA/AML: Incident reporting integrated with AML program integrity
Meeting those timelines requires more than intent — your policy must document the mechanics:
- Detection and escalation procedures
- Containment and recovery protocols
- Notification timelines with role-specific responsibilities
- Documentation and post-incident review processes
Data Classification and Retention
Policies must specify how data is categorized (public, internal, confidential, restricted), retention periods, and secure disposal:
- BSA requirements: 5-year retention under 31 CFR 1010.430
- GDPR Article 17: Right to erasure balanced against legitimate retention needs
- Industry-specific mandates: Payment card data retention limits under PCI DSS
Generic policy templates rarely address retention correctly — regulators routinely find gaps here during examinations.
Enforcement and Consequences
Compliance frameworks require documented disciplinary procedures for policy violations. Without enforcement mechanisms, regulators view policies as "paper exercises."
Auditors will look for:
- Defined consequences for policy violations
- Annual employee attestation (signed acknowledgment)
- Training completion records
- Monitoring and audit evidence
AICPA SOC 2 (Criteria CC2.2) and ISO/IEC 27001:2022 (Clause 7.3) require documented evidence that employees have read and understood security policies.
How to Develop a Security Policy for Compliance: Step-by-Step
Step 1: Conduct a Risk Assessment and Regulatory Inventory
Before drafting policies, identify: This inventory anchors every policy decision to your actual risk profile — not a generic template.
- Applicable regulatory obligations (BSA/AML, GDPR, PCI DSS, NYDFS, Reg E)
- Specific risk environment (data types, third-party dependencies, geographic footprint)
- Known threat vectors
- Current control gaps
NIST SP 800-37 specifies that risk assessment results inform security requirements definition, categorization decisions, and control selection. This dual inventory shapes every policy decision that follows.
Step 2: Define Your Policy Architecture
Choose between a single master security policy and a layered framework. For early-stage fintechs, a prioritized set of 6-10 core policies is more practical than attempting comprehensive coverage:
- Acceptable Use Policy
- Access Control Policy
- Incident Response Policy
- Data Classification Policy
- Vendor Management Policy
- Remote Access Policy

Step 3: Draft With Compliance Alignment in Mind
Each policy should reference specific regulatory requirements or control frameworks it satisfies. For example: "This access control policy supports compliance with NIST 800-53 AC-2 and PCI DSS Requirement 7."
Explicit mapping provides:
- Efficient audits and due diligence reviews
- Demonstration of mature governance
- Clear traceability between controls and requirements
- Simplified evidence gathering
Step 4: Engage Stakeholders and Subject Matter Experts
Cross-functional input ensures policies are both technically feasible and legally sound:
- IT confirms what controls are technically implementable
- Legal/Compliance Counsel validates regulatory alignment
- HR reviews employee-facing language for clarity and enforceability
- Executive Leadership formally approves policies — a hard requirement under many audit frameworks
For companies without full-time compliance officers, fractional compliance leadership—such as Fraxtional's fractional CCO or BSA Officer services—provides critical expertise to ensure policies withstand regulatory scrutiny from day one.
Step 5: Implement, Train, and Obtain Attestation
Effective rollout goes beyond document distribution:
- Employee training programs
- Signed acknowledgment records (attestations)
- Integration into onboarding processes
- Documented training completion
Auditors routinely request training records and attestations as evidence in SOC 2 audits, ISO 27001 assessments, and bank examinations.
Step 6: Monitor, Test, and Update Annually
Security policies are living documents. ISO/IEC 27001:2022 Clause 10.1 requires continual improvement of the ISMS. NYDFS Part 500 mandates periodic risk assessments updated as necessary to address changes.
Review triggers include:
- Regulatory changes
- Material security incidents
- Significant business changes (new products, acquisitions)
- Annual compliance calendar milestones
Without a structured review cadence, policies drift from operational reality — creating gaps that examiners and auditors are trained to find.
Mapping Security Policies to Key Compliance Frameworks
Mapping Security Policies to Key Compliance Frameworks
Each major compliance framework carries distinct security policy requirements. Understanding how your policies map to each one prevents gaps that examiners and auditors will find.
NIST 800-53: Comprehensive Control Baseline
NIST SP 800-53 Revision 5 provides a comprehensive control catalog that financial regulators and sponsor banks treat as baseline:
- Access Control (AC): User access policies, least privilege, session controls
- Audit and Accountability (AU): Audit logging, monitoring, review procedures
- Incident Response (IR): Detection, reporting, containment, recovery
- Planning (PL): Security planning, system security plans, rules of behavior
- System and Information Integrity (SI): Flaw remediation, malicious code protection, monitoring
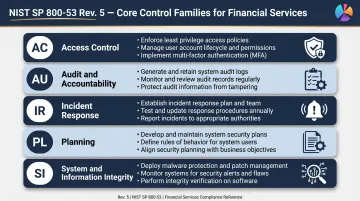
Sponsor banks routinely ask fintech partners to demonstrate coverage across AC, AU, and IR as a baseline condition for partnership approval.
BSA/AML: Security as AML Program Integrity
FinCEN assessed a $37 million penalty against Paxful for failing to implement basic security and monitoring policies, prosecuted as AML program violations. The FFIEC BSA/AML Examination Manual states that internal controls include policies and procedures designed to manage ML/TF risks and achieve BSA compliance.
Required security policy elements:
- Data access controls protecting customer information
- Suspicious activity monitoring system security
- Staff training on security measures
- Integration with AML program governance
In practice, this means your SAR filing procedures, system access logs, and security incident response protocols should all reference your AML governance structure — not exist as separate documents.
GDPR: Technical and Organizational Measures
Any company processing EU resident data must maintain documented technical and organizational measures (TOMs):
- Data security policies covering encryption and access controls
- Breach notification procedures (72-hour timeline under Article 33)
- Data minimization and purpose limitation
- Roles of Data Controller and Data Processor
- Data Processing Agreements with vendors
GDPR Articles 28 and 32 mandate that processing by processors be governed by contracts specifying security measures.
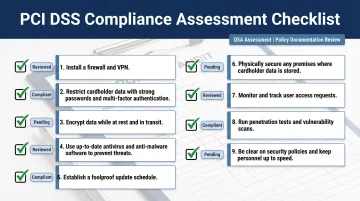
PCI DSS: Mandatory Policy Documentation
PCI DSS v4.0.1 Requirement 12 mandates formal information security policies:
- Annual review and updates
- Communication to all relevant personnel
- Operational security policies covering all 12 PCI DSS requirements
- Clear definition of information security roles and responsibilities
- Employee acknowledgment of responsibilities
Requirement 12 is often the first finding in a QSA assessment — not because companies lack security controls, but because those controls aren't formally documented, reviewed annually, or acknowledged by staff in writing.
Common Mistakes That Undermine Security Policy Compliance
The "Copy-Paste Policy" Problem
Organizations downloading generic templates adopt policies referencing wrong systems, irrelevant regulations, or non-existent roles. Regulators and auditors immediately identify templated policies that haven't been operationalized.
That gap has real consequences. NYDFS fined GEICO for failing to implement written policies addressing application development and customer data privacy — a clear example of how generic approaches collapse under regulatory scrutiny.
The "Set It and Forget It" Failure
Policies unchanged for over a year are frequently cited as deficiencies in bank examinations and regulatory reviews. Regulatory guidance evolves constantly — updated NYDFS Part 500 requirements, new BSA examination guidance — and active policy maintenance is expected, not optional.
The Enforcement Gap
Regulators look for evidence of policy enforcement:
- Training logs
- Access reviews
- Incident reports
- Disciplinary records
For fintech and crypto companies, absence of enforcement evidence is more damaging than having no written policy, because it signals performative compliance culture. Fraxtional embeds experienced compliance directors into fintech and crypto teams to keep policies enforced, tested, and audit-ready — without the cost or commitment of a full-time hire.
Frequently Asked Questions
How to ensure compliance with security policies?
Compliance with security policies requires employee training and attestation, defined enforcement consequences, regular internal audits or policy reviews, and continuous monitoring. Assigning clear ownership—such as a CCO or compliance officer—to each policy area is essential for accountability and demonstrating governance maturity to regulators.
What are security policies and procedures?
Security policies are high-level governance documents establishing rules, roles, and objectives. Security procedures are step-by-step operational instructions implementing those rules. Both are necessary for compliance: policies define the "what," procedures define the "how," and together they demonstrate that controls are documented and repeatable.
What are examples of information security policies?
Key examples include Acceptable Use Policy, Access Control Policy, Data Classification Policy, Password Management Policy, Incident Response Policy, Remote Access Policy, and Vendor Management Policy. The specific set required varies by regulatory framework, industry, and business model—fintech companies handling payment card data require PCI-specific policies.
What are the 5 key areas of compliance?
The five generally recognized areas are: regulatory adherence, risk management, internal controls, training and awareness, and monitoring and auditing. A mature security policy framework supports each area with documented evidence showing how policies translate into operational controls.
Is NIST 800-53 a compliance standard?
NIST 800-53 is a security control catalog developed by the National Institute of Standards and Technology, not a certification standard. It is widely used as a compliance baseline by federal agencies, financial regulators, and sponsor banks evaluating fintech security programs—with many regulatory frameworks referencing its controls as acceptable implementation guidance.
What are the three pillars of the CIA triad?
The CIA triad covers three principles: Confidentiality (blocking unauthorized data access), Integrity (preventing unauthorized modification), and Availability (ensuring systems remain accessible when needed). Security policies are designed to preserve all three, with each mapping to specific regulatory requirements.